I thought deleting an app deleted everything. I was wrong. Most people are wrong about this. And in a federal courtroom in Texas during the Prairieland case involving a woman, Lynette Sharp, and an attack on a Texas detention center in July 2025, that misconception just became evidence.
During the recent trial in March 2026, the FBI was able to use tools like Cellebrite to forensically extract data and copies of incoming Signal chat messages from a defendant’s iPhone, even after the app had been deleted, because copies of the message content were saved in the device’s push notification database. As per 404Media, the case involved defendant Lynette Sharp, who had already removed Signal from her phone.
For the investigators, that didn’t matter. The messages were still there, quietly sitting in Apple’s internal notification cache storage.
Here’s the part that I think a lot of people are going to miss.
Signal does not send message content to Apple’s servers. Instead, messages are decrypted locally on the device before generating notifications. When lock screen previews are enabled, iOS caches that content in internal storage, which then survives app deletion.
In this scenario, Signal’s encryption did its job perfectly. It was the operating system itself that acted as a weak point. That’s a completely different problem, and one that no amount of end-to-end encryption can solve on its own.
I find this genuinely unsettling. Most people enable notification previews because they’re convenient. You glance at your lock screen, see the message, and then and there decide if it’s urgent. But many aren’t aware that this convenience is quietly building a database of their conversations in a place most people don’t even know exists.
An important aspect to remember is that only incoming messages were recoverable through this method. Outgoing messages were not captured. So, it is just half the conversation, but still enough to use in court.
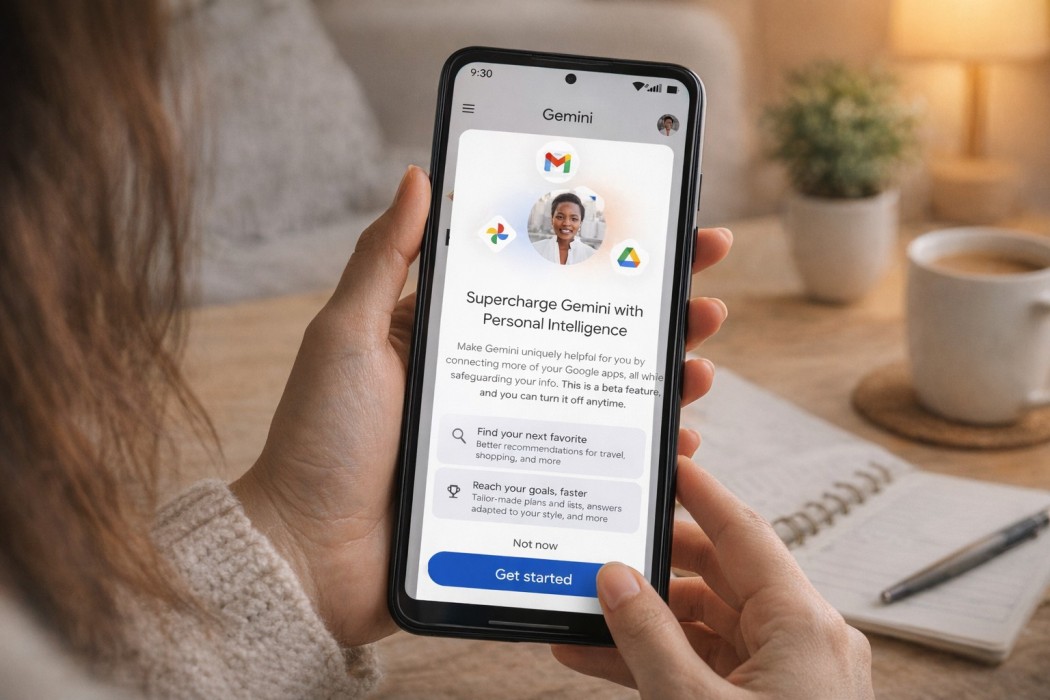
For those of you who are wondering, the fix is simple, and you should do it right now.
Open Signal, go to Settings, then Notifications, then Notification Content, and select “No Name or Content.” Also, go to your iPhone’s Notification Settings for Signal and set Show Previews to Never. Once done, your phone will still alert you when a message arrives; however, it won’t store the actual message.
This vulnerability presumably isn’t exclusive to Signal, so if you are concerned about your privacy, then you might want to turn off similar preview settings in other messaging apps.